There are four types of parking lots at BYU: Faculty and Staff Parking, Graduate Student Parking, Undergraduate Student parking, and Visitor Parking. Because faculty parking lots are everywhere on campus, while graduate student and undergraduate student parking lots are relatively further away from the center of the campus (graduate parking lots are slightly closer), many students are tempted to park at faculty parking lots just briefly for a class period of about one-hour. Many used to be able to get away from it because of limited parking officers, but that is probably coming to an end because campus police has a better weapon to fight parking violators.
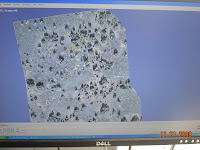
 An automatic license plate recognition system, developed in Israel (I suspect this company) and made its way into US through Canada (don't ask me why), has become a very powerful tool for BYU police to catch parking violators. Cameras installed on top of police cars (as shown in the picture on the left) can automatically take pictures of cars in the parking lots. License plates are recognized and matched against a database to quickly determine if the car can park at the parking lot. An alarm is played when a violator is identified, and with just a push of a button, a parking ticket is automatically generated and printed. Parking officers can now quickly drive around campus multiple times each day and get their job down all with the comfort of sitting in their seats.
An automatic license plate recognition system, developed in Israel (I suspect this company) and made its way into US through Canada (don't ask me why), has become a very powerful tool for BYU police to catch parking violators. Cameras installed on top of police cars (as shown in the picture on the left) can automatically take pictures of cars in the parking lots. License plates are recognized and matched against a database to quickly determine if the car can park at the parking lot. An alarm is played when a violator is identified, and with just a push of a button, a parking ticket is automatically generated and printed. Parking officers can now quickly drive around campus multiple times each day and get their job down all with the comfort of sitting in their seats.The picture on the
 right shows a closer view of the type of camera in use. The same kind of camera is also used at gated areas to automatically raise the gate for eligible cars. The accompanying software can read 60 plates a second and can recognize a license plate on a car going 120 mph with the help of the high-speed camera and fast computer algorithms in recognizing numbers and letters. The system also a GPS built-in, so images of cars are also geo-tagged with GPS locations in case people forget where they parked their cars.
right shows a closer view of the type of camera in use. The same kind of camera is also used at gated areas to automatically raise the gate for eligible cars. The accompanying software can read 60 plates a second and can recognize a license plate on a car going 120 mph with the help of the high-speed camera and fast computer algorithms in recognizing numbers and letters. The system also a GPS built-in, so images of cars are also geo-tagged with GPS locations in case people forget where they parked their cars.Inside the police car, a very durable tablet PC is mounted on the panel so the parking officer can interact with the software using a stylus pen. A wireless keyboard can also be used to enter license numbers into the system.
Obvious benefits of the system include: more efficient patrol of lots of
 parking lots, comfort of staying in the car in extreme weathers (hot or cold), and automatic alert for stolen vehicles. However, this technology also has its drawbacks. For example, in cases of heavy snow (which is not so rare in Utah), the license plate might be covered by snow and not visible. Also since the parking officers can now do most of their job without getting out of the car, special parking spots like the 15-minutes ones are getting less attention and could be abused more frequently. In the past, people who owned multiple vehicles had the option of hanging a badge in one of the cars. This also means only one car is allowed to be parked on campus because there is only one badge. With the new system, since there's no sticker and no badge, all cars can be parked on campus at the same time. Lastly, privacy is also a concern because now the campus police can easily identify when cars are parked where each day.
parking lots, comfort of staying in the car in extreme weathers (hot or cold), and automatic alert for stolen vehicles. However, this technology also has its drawbacks. For example, in cases of heavy snow (which is not so rare in Utah), the license plate might be covered by snow and not visible. Also since the parking officers can now do most of their job without getting out of the car, special parking spots like the 15-minutes ones are getting less attention and could be abused more frequently. In the past, people who owned multiple vehicles had the option of hanging a badge in one of the cars. This also means only one car is allowed to be parked on campus because there is only one badge. With the new system, since there's no sticker and no badge, all cars can be parked on campus at the same time. Lastly, privacy is also a concern because now the campus police can easily identify when cars are parked where each day.So how does the recognition work? There are two main challenges: 1. Identify the license plate in the picture. 2. Recognize the license number. I don't know the exact algorithms used in the system, but based on techniques learned form my computer vision class, I certainly can come up with some intelligent guesses. Identifying the license plate in a picture probably relied on edge detection techniques combined with detecting high-contrast areas that also have the rectangular or rhombus shape. A coarse to fine search is also likely. Recognizing the letters and numbers is relatively easy with machine learning classification algorithms such as decision tree or nearest neighbor.
It is worth mentioning that such license plate recognition systems are already widely used by police forces. The video below shows an example. If you live in California, then you probably have heard stories where people get their traffic ticket in the mail together with a picture of their license plate. A friend of mine told me that once he actually received a ticket in the mail together with a link. Following the link, he was able to view a video of himself making a right turn without making a complete stop. How amazing!
A BYU parking officer said the following in an interview:
"With the money we saved in parking sticker costs, we were able to buy the car."
What I probably would add to that is: "With the extra parking tickets we were able to write, I am expecting a much bigger bonus!" Just kidding!
Picture of the Day:
Google street view uses facial recognition software agent to detect faces in photos and then blur them for privacy protection. The software agent dutifully blurred hunger striker Bobby Sandss's face in a street portrait in Belfast. (Click the picture to see more!)